Many people have this interest in cryptocurrencies far beyond transacting overseas, online shopping, or even playing at the best crypto casino. If you do your crypto research, the phrase Merkle Tree Blockchain may have popped up, leaving you wondering what that is about.
Merkle Trees are a driving force behind blockchain technology’s success. But, they are not a widely-understood concept amongst many in the crypto industry.
Simply put, a Merkle Tree Blockchain is a manner of structuring data that enables a lot of information to be quickly verifiable for accuracy. Read on as we take a closer look at Merkle Tree Blockchains and how they impact the crypto world.
What Is a Merkle Tree?

To understand Merkle Trees a little better, we must first analyse the problem they solve. You can access information from a single copy at the core of a centralised network. It means that there isn’t much required to store or access data.
However, things can get complicated with a decentralised blockchain network whenever new information is copied among nodes. It’s challenging to access and copy and share information among nodes efficiently. All this happens while ensuring that the shared information is verified for each receiving node.
To address this problem, Merkle Trees help decentralised blockchains to share information, verify it, and make it trustworthy. Merkle Trees organises data without much processing power to share and confirm that data. In addition, it facilitates secure transactions by using hash functions and cryptography.
History and Origin Of Merkle Trees
While Satoshi Nakamoto was the first to use Merkle Trees in blockchain technology with Bitcoin, the concept was first introduced in 1979 by Ralph Merkle. Merkle wrote a paper called “A Certified Digital Certificate” and, in the process, unknowingly created a significant component of blockchain.
In this paper, Merkel described a new technique for creating proofs. He designed a process for verifying data that would enable computers to work much more quickly than ever before. This concept was named the Merkle Tree. It’sIt’s a ground-breaking technique that changed how cryptography works, including how encrypted computer protocols operate.
Merkle Trees have become popular in recent years in both Bitcoin and Ethereum’s foundational codes. Therefore, it is essential to understand blockchains to understand Merkle Trees better and how they impact the network.
Blockchains are made up of hundreds of thousands of blocks that can each hold thousands of transactions. Each transaction on a blockchain has a unique transaction ID – usually a 64-character code that takes 32 bytes of memory. With this in mind, computing power and memory space become critical for efficiency and security.
That said, using as little data as possible when processing and verifying transactions on the network is beneficial. It is to reduce CPU processing times and provides added security. It is where Merkle Trees come into play. They take many transaction IDs and send them through a mathematical process that results in one 64-character code – called a Merkle Root.
Merkle Root Explained
The Merkle Root is important. It authorises any computer to verify that a specific transaction occurred on a particular block as precisely as possible. However, to better understand a Merkle Root, we must first understand hashing.
Hashing functions are mathematical algorithms that take inputs and deliver outputs. Standard hashing functions include MD5, SHA-3, and SHA-256. As mentioned above, the Merkle Tree’sTree’s single code is called a Merkle Root, with every individual block having one.
Merkle Tree always groups all of the data input into pairs. The last input is copied and paired with itself when there is an odd number of inputs. It applies to all transaction IDs written on a block in a blockchain.
For example, if a single block has 420 transactions, the Merkle Tree would group these into 210 pairs. These would then go through a hashing function, resulting in 210 new 64-character codes. The process continues, and the 210 new codes will be paired again into 105 pairs. From there, the cycle repeats once more, halving the number each time. Finally, a single code remains ؘ– the Merkle Root.
How Do Merkle Trees Work?
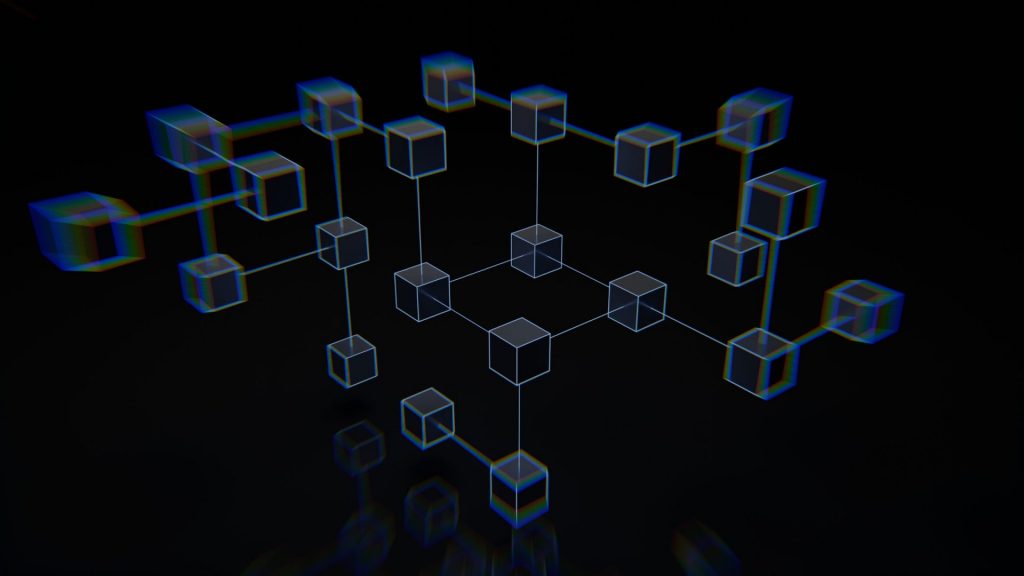
Merkle Trees are data structure trees where the non-leaf mode is defined as a hash value of its respective child nodes. The Merkle Tree is inverted down, where the leaf nodes are the lowest.
When looking at a Merkle Tree, you will find that it can be described as an upside-down tree capable of summarising an entire set of transactions independently. With this structure, a user can verify if a transaction is part of the block or not. For Merkle Trees to be effective, hashing must be used.
Merkle Trees are created from the bottom up using individual transaction hashes known as transaction IDs. The leaf nodes are the nodes that contain transactional data hashes. In the case of the non-leaf nodes, they store the hashing algorithms of the previous two hashes.
Merkle Trees are binary. It means it requires leaf nodes to be even for them to work. As mentioned above, in the case of an odd number of leaf nodes, the hash will duplicate the last hash to make it even.
Merkle Tree in Blockchain
To understand how vital Merkle Trees are for blockchain technology, all we need to do is imagine the landscape of blockchain technology without any Merkle Trees. To illustrate this point, we will refer primarily to Bitcoin and, to a lesser extent, Ethereum. Merkle Trees are pivotal to both those cryptocurrencies.
Bitcoin
If Bitcoin didn’t have any Merkle Trees, every node on the network would need to keep a complete copy of every transaction that has ever occurred on the blockchain. Imagine how much information that would be to store and digest.
When confirming a previous transaction, a node must reach out to the network to acquire copies of the ledger from its peers. Once done, the node needs to compare each entry, line by line, to ensure that its records and the network records are an exact match. If there are discrepancies between ledgers, it can compromise the network’s security. These are the very situations that hackers wait patiently for.

Verification requests on Bitcoin would entail copious amounts of information being sent over the network. It is because you would need to have the data before validating it. The computer used for validating would require a large amount of processing power to compare such significant ledgers to ensure no changes or discrepancies.
Merkle Tree is the perfect solution for Bitcoin as they hash the records in the ledger. In effect, this separates the proof of data from the data itself. Using Merkle Trees to prove a valid transaction is as simple as sending a tiny bit of information across the network. Moreover, it enables users to prove that both ledger versions are identical, requiring a fraction of computer power and network bandwidth.
Ethereum
In terms of Ethereum, Merkle Trees are used in a more complicated manner. A block in the Ethereum blockchain has a header, a list of transactions, and a list of uncle blocks. The process is known as the Merkle Patricia Tree and uses three different Merkle Roots for each block.
The header includes a transaction root hash that validates the list of transactions. While transactions are sent over the network from peer-to-peer as a simple list, they must be assembled into a particular data structure. This structure is known as a trie to compute the root hash.
This structure is only needed to verify blocks. It can be discarded once the block has been verified. Transaction lists are kept locally in a trie and serialised to lists to send to clients requesting the blockchain. Ethereum’s home-rolled encoding system – Recursive Length Prefix Encoding (RLP) – encodes all entries in the trie.
Cryptographic Hash Functions
As you may have gathered, cryptographic hash functions are a necessary part of Merkle Trees. A hash function is primarily responsible for mapping any arbitrary information of any length to a fixed-size output. It operates as a cryptographic function and is widely used in cryptography.

Hash functions are known to be very efficient and operate as a one-way functions. It means there is no reversing them. It is designed to work as one-way only and has multiple uses, including password protection, file integrity and verification, and cryptocurrency.
There are many different families available, and these include Message Direct(MD), Secure Hash Function(SHF), and RIPE Message Direct(RIPEMD). The key properties of hash functions include:
- Deterministic
- Pre-image resistant
- Computationally efficient
- Cannot be reverse-engineered
- Collision resistant
While cryptographic hash functions are interesting, their elements are complicated. It can make it tricky to grasp if you are not technically minded. That said, we will not delve much deeper into cryptographic hash functions in this article.
Benefits of Merkle Trees
There are many benefits that a Merkle Tree Blockchain can offer. Let’sLet’s discover some of their most striking advantages.
Efficient Verification
Merkle Trees offer efficient verification of integrity and validity of information on the network. In addition, it reduces the amount of memory needed for these verification checks to be complete.
Proof verification requires only minimal information to be transmitted across the blockchain network. Moreover, it enables a trustless cryptocurrency transfer in a peer-to-peer, distributed system by quickly verifying transactions.
No Delays
There will be no delays when transferring information across the network using Merkle Trees. In addition, Merkle Trees are used widely in computations that maintain the function of cryptocurrencies.
Save on Storage
Merkle Trees occupy much less disk space when considering the space requirements of other data structures.
Accurate Transfer of Information
Merkle Root is beneficial in ensuring that the blocks sent across the network are accurate, unchanged, and whole.
Tamper Detection
All transactions stored in a Merkle Tree store the hash of each node in the upper parent node. Changes in a transaction’s details will filter to the hashes in the upper levels and eventually to the Root. Merkle Trees allow miners to confirm if any transactions have been tampered with.
Miners can compare the Merkle Root in the headers with the Merkle Root stored in the data part of a specific block. It enables them to find out if there was tampering with information.
Simple Payment Verification (SPV)
It is a way to verify transactions in a block without downloading the entire blockchain. In this case, a user will only need a copy of the block header of the longest chain. The copy of the block header is stored in the SPV wallet that uses the SPV client to link a transaction to a Merkle branch in a block.
Without getting into the complexities of SPV operations, the fact that you can verify transactions quickly and accurately is one of the significant advantages of Merkle Trees. The SPV client can request proof of inclusion through a Merkle branch. If the transaction can be linked to a Merkle branch, that is proof that the transaction exists.
Final Thoughts
One would struggle to imagine how the world of cryptocurrencies and blockchain technology would have survived had it not been for the innovation of Merkle Trees. It is especially true considering the incredible amounts of computing power and storage space it saves.
Remarkably, an idea conceived in 1979 – almost 43 years ago – would serve as the cornerstone for what many consider the future of technology and finance globally.
Merkle Trees are crucial for blockchains. They allow them to operate effectively while maintaining transaction integrity. Time will tell whether developers can further exploit Merkle Trees’s wonders to enhance this new age of technology and digital assets.